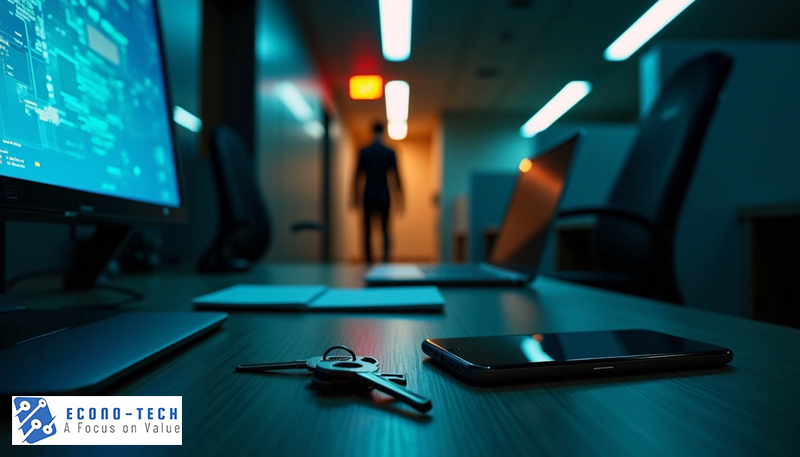
Even though most companies invest in security onboarding, offboarding security risks remain, which can cost organizations greatly. Departing employees retain access to data and credentials long after the final day of work. Malicious actors can exploit these vulnerabilities. Businesses focus on protecting their company data from external threats but overlook the security gaps that emerge during employee exits. Why should you reevaluate security risks when offboarding? The answer becomes clear when we look at the potential for data theft, unauthorized access, and intellectual property loss. This piece explores the security vulnerabilities hiding in your exit process and provides practical strategies to protect your organization.
Understanding Why Offboarding Security Matters
When an employee departs from the business, it creates a unique security window that differs from other known security threats. Companies invest considerable resources in strengthening their data security; however, internal pathways can bypass those protections. When the employee departs, they already possess legitimate credentials, system knowledge, and data system setups. This will present a different risk profile than external attackers.
The timing of the employee’s exit will amplify these risks. There is a short distance between the employee’s resignation announcement and their final departure. Some employees’ motivation changes and often weakens. Although some employees will maintain a positive relationship with the business and leave with grace. On the other hand, there is one that harbors grievances or competitive intentions, which leads to unauthorized data collection.
Access persistence creates the largest vulnerability. Computer accounts, passwords, vpn credentials, and system permissions are still with the employee. The employee retains access to email systems, cloud storage, customer information, and proprietary tools for days, weeks, and sometimes months after leaving the company.
This extended access window provides plenty of opportunity for data theft or system compromise.
Sometimes, managers will hesitate to revoke access rights right away. They may fear a disruption to ongoing projects or knowledge transfers. This hesitation will extend the vulnerability window, increasing the company’s exposure to both intentional and accidental security breaches.
Common Offboarding Security Vulnerabilities
Several vulnerabilities emerge when companies fail to address offboarding security risks. Orphaned accounts are one of the most widespread problems. This is from former employees who maintain directory accounts, email addresses, and application login information that continue to function. Attackers love to scan and find inactive accounts with valid permissions.
Shadow IT access compounds the problem. Some employees may leave but use unauthorized applications that IT departments have never documented. Without a detailed application inventory, the IT team cannot revoke access. This also allows the employee to maintain access to project management tools that fall outside the official IT Department oversight.
Shared credentials create a whole other problem. Teams often share passwords, analytics, or even vendor portals. When an employee leaves, changing these shared credentials requires coordination with multiple team members. Organizations postpone or forget this step .
Another risk is Laptops, mobile devices, and key cards. These contain sensitive information and must be retrieved, and the data cleaned/erased. Personal devices with company data access would require remote wiping on the last day of employment. Unfortunately, many companies lack the enforcement to implement it.
How to Protect Your Organization During Employee Exits
Protecting your organization requires structured protocols before employees announce their departure. You need to create a comprehensive offboarding checklist documenting every system, application, and resource that requires access revocation. This checklist should include both IT-managed and shadow IT applications that employees use.
Immediate access restriction becomes necessary once an employee submits their resignation. The IT department should disable all remote access and VPN credentials within hours of giving notice.
Deactivation of accounts must be scheduled. Administrative privileges should be revoked right away. Email access should be removed within 24 hours of departure. On the final working day, cloud storage, all databases, and team tools must be deactivated. This prevents former employees from exploiting access windows to extract data.
Company asset recovery also needs attention. Company laptops, mobile devices, security badges, and any other hardware containing company data must be collected before the employee leaves the building.
Exit interviews that address security protocols need to happen. Document all accounts the departing employee accessed, including any personal tools they used for work. This information helps you identify gaps in your offboarding security risks management and prevents future vulnerabilities from emerging undetected.
Conclusion
Offboarding security risks need the same attention you give external threats. Departing employees can create vulnerabilities that can last long after their final workday. However, most organizations lack an exit plan for their data. Have detailed checklists for each of the above-mentioned steps and treat departures as potential security events. Your offboarding process isn’t just an HR formality. It’s a crucial security control that protects your whole organization.
Offboarding Security Risks | Blog Article | Econo-Tech | All Rights Reserved | Farmingdale, NY